Using Dev Proxy in your GitHub Actions workflow on macOS
This post is over a year old, some of this information may be out of date.
Lately, I have been working with the Microsoft’s Dev Proxy, a tool for API simulation, mocking, and testing. One of the things I wanted to try was to use the Dev Proxy in a GitHub Actions workflow so that I could use it in combination with Playwright to test my solutions with mocked APIs.
The Dev Proxy is a .NET Core application that can run on any platform that supports .NET Core, so it works on Windows, Linux, and macOS. I chose to use a macOS virtual machine/runner because, at the time of writing, the Dev Proxy cannot automatically trust the root certificate.
In this blog post, I will show you how to use the Dev Proxy in your GitHub Actions workflow on a macOS virtual machine.
Installing the Dev Proxy
Let us start with installing the Dev Proxy on the macOS virtual machine. We can use the bash script provided in the Dev Proxy documentation for this. To include this into your GitHub Actions workflow, you can use the following step:
- name: Install Dev Proxy run: bash -c "$(curl -sL https://aka.ms/devproxy/setup.sh)"Running the Dev Proxy as a background service
Once installed, you can run the Dev Proxy as a background service by adding an ampersand & at the end of the command.
Here is what the GitHub Actions step looks like:
- name: Run Dev Proxy run: ./devproxy/devproxy &What about HTTPS endpoints?
When you start using the Dev Proxy like this on GitHub Actions, you will encounter issues when calling HTTPS endpoints. In my case, I got the following error when testing it with Playwright:
Error: page.goto: net::ERR_PROXY_CONNECTION_FAILED at https://frontmatter.codes/These issues are normal because to intercept HTTPS traffic, you must trust the root certificate which gets created by the Dev Proxy. When you run the Dev Proxy on your local machine for the first time, it will prompt you to trust the root certificate.
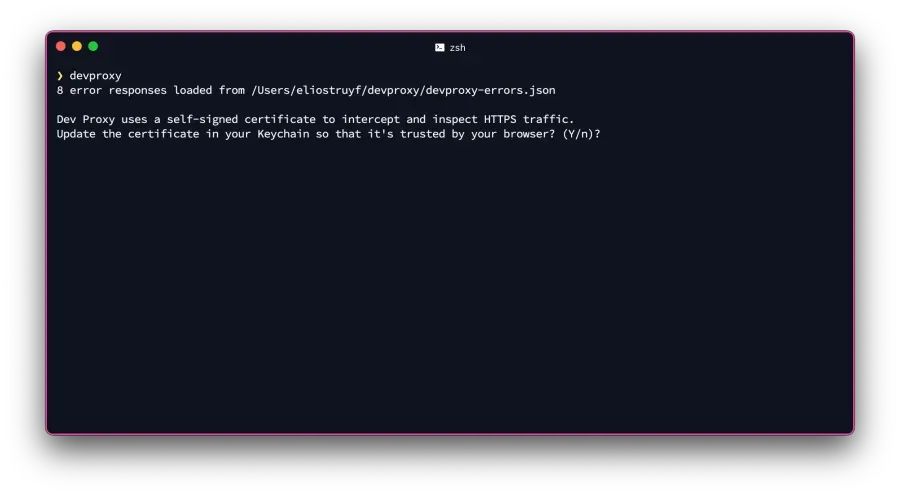
As it runs in a non-interactive mode in GitHub Actions, you cannot trust the certificate that way. To solve this, we will have to include a couple of extra steps in our workflow to trust the root certificate and be able to intercept the HTTPS traffic.
Trusting the root certificate
When the Dev Proxy asks you to trust the root certificate, and you accept it, it uses the trust-cert.sh script to find the certificate and trust it.
My first attempt was to run the trust-cert.sh script in my GitHub Actions workflow. Unfortunately, this did not work because the security add-trusted-cert command requires a password to add the certificate to the login keychain.
After some research, I found an article about Trusting Certificates in System Keychain without Prompting. The article explains that you will not be prompted for a password when you add a certificate to the system keychain, and this will be our solution to make it work in our GitHub Actions workflow.
The script to trust the certificate in the system keychain looks as follows:
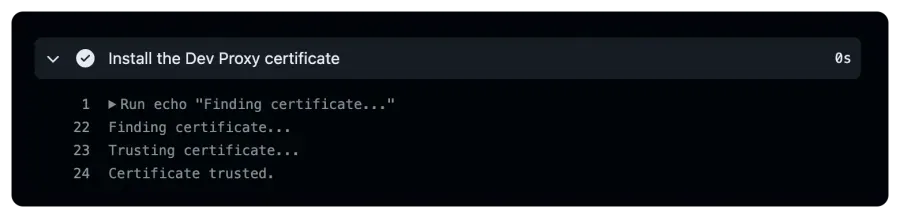
- name: Install the Dev Proxy's certificate timeout-minutes: 1 run: | echo "Finding certificate..." security find-certificate -c "Dev Proxy CA" -a -p > dev-proxy-ca.pem
echo "Trusting certificate..." sudo security add-trusted-cert -d -r trustRoot -k /Library/Keychains/System.keychain dev-proxy-ca.pem echo "Certificate trusted."
# Set the system proxy settings (optional) echo "http_proxy=http://127.0.0.1:8000" >> $GITHUB_ENV echo "https_proxy=http://127.0.0.1:8000" >> $GITHUB_ENV
# Required to test CURL with the Dev Proxy (optional) echo "SSL_CERT_FILE=$GITHUB_WORKSPACE/dev-proxy-ca.pem" >> $GITHUB_ENVThis script is similar to the trust-cert.sh script, but instead of adding it to the login keychain, the certificate gets added to the system keychain.
At the end of the script there are three exports which are all optional.
- The
http_proxyandhttps_proxyenvironment variables can be used to set the system proxy settings on the macOS virtual machine. - The
SSL_CERT_FILEenvironment variable is required on macOS to make thecurlcommands work with the Dev Proxy.
The complete GitHub Actions workflow
Now that we have the certificate trust figured out, we can combine all the steps into a complete GitHub Actions workflow.
name: macOS Dev Proxy
on: push: branches: - main - dev workflow_dispatch:
jobs: test: timeout-minutes: 60 runs-on: macos-latest steps: - uses: actions/checkout@v4
- uses: actions/setup-node@v4
- name: Install Dev Proxy run: bash -c "$(curl -sL https://aka.ms/devproxy/setup.sh)"
- name: Run Dev Proxy run: ./devproxy/devproxy &
- name: Install the Dev Proxy's certificate timeout-minutes: 1 run: | echo "Finding certificate..." security find-certificate -c "Dev Proxy CA" -a -p > dev-proxy-ca.pem
echo "Trusting certificate..." sudo security add-trusted-cert -d -r trustRoot -k /Library/Keychains/System.keychain dev-proxy-ca.pem echo "Certificate trusted."
# Set the system proxy settings (optional) echo "http_proxy=http://127.0.0.1:8000" >> $GITHUB_ENV echo "https_proxy=http://127.0.0.1:8000" >> $GITHUB_ENV
# Required to test CURL with the Dev Proxy (optional) echo "SSL_CERT_FILE=$GITHUB_WORKSPACE/dev-proxy-ca.pem" >> $GITHUB_ENV
# Include the additional steps you want to run after the Dev Proxy started - name: Test Dev Proxy run: | curl -ix http://127.0.0.1:8000 https://jsonplaceholder.typicode.com/posts # When you used the system proxy settings, you don't need to specify the proxy in the curl command curl -i https://jsonplaceholder.typicode.com/posts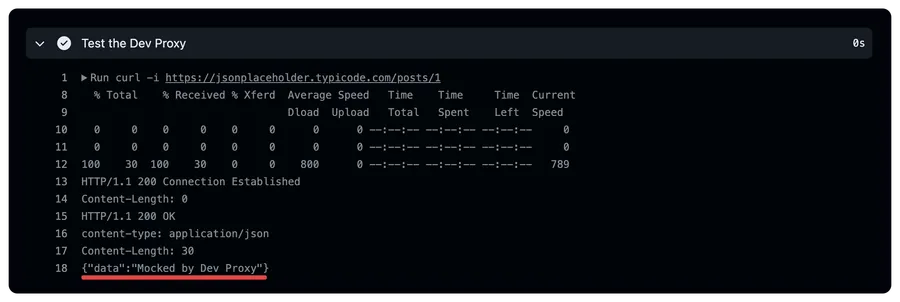
With this setup, you can use the Dev Proxy in your GitHub Actions workflow on a macOS virtual machine. This allows you to use the Dev Proxy in combination with Playwright or any other tool for testing your solutions.
Related articles
Using Dev Proxy in your GitHub Actions workflow on Ubuntu
Learn how to use Dev Proxy in a GitHub Actions workflow on an Ubuntu hosted VM for intercepting and inspecting your API calls
Caching Dev Proxy in your GitHub Actions workflows
Learn how to cache the Dev Proxy in your GitHub Actions workflows. This allows you to reuse the Dev Proxy installation and speed up your workflow.
Use Playwright with Microsoft Dev Proxy on GitHub Actions
Learn how to use Playwright with Microsoft Dev Proxy on GitHub Actions to easily test your solutions with the same mocked API responses as during development.
Report issues or make changes on GitHub
Found a typo or issue in this article? Visit the GitHub repository to make changes or submit a bug report.
Comments
Let's build together
Manage content in VS Code
Present from VS Code
